IJCST ONLINE
DOWNLOADS
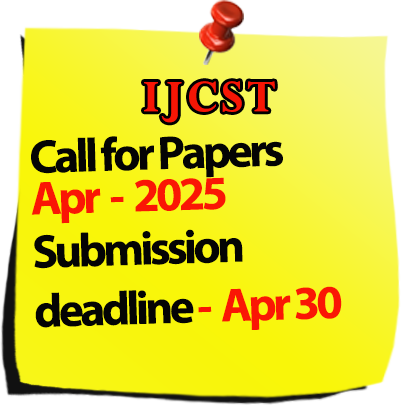
Call for Paper :

Welcomes Conference Proposals

International Journal of Computer Science Trends and Technology
IJCST-Volume 4 Issue 1 / Jan - Feb 2016
|
S.No
|
Title/Author Name
|
Page No
|
|
1
|
How Wireless Security Can Be Compromised
- Shripal Rawal Abstract |
1 |
|
2
|
Big Data Analytics: Challenges and Solutions Using Hadoop, Map Reduce and Big Table
- M. Dhavapriya, N. Yasodha Abstract |
5 |
|
3
|
Preventive System for Forests
- Prasad R. Khandar, K. Deivanai Abstract |
15 |
|
4
|
Digital Video Monitoring System Based On ARM Cortex A7
- R. R. Karhe, Gayatri P Sonawane Abstract |
19 |
|
5
|
Symmetric Encryption Scheme Using Logistic Map
- K.Saranya, AG.Shanmathi, N.Suchitra, Dr.S.Ramakrishnan Abstract |
23 |
|
6
|
A Comparative Study of Disk Scheduling Algorithms
- Tarsem Singh Abstract |
29 |
|
7
|
A Survey on Bug Triaging With Software Data Reduction
- KrishnaVeni V.L, Karthik.M Abstract |
33 |
|
8
|
A Glimpse of Software Quality Assurance and Factors Affecting It
- Divya C D, Bharath T S Abstract |
37 |
|
9
|
A Study: Network Technologies for Rural Regions
- Sanjib Das, Nikita Baidya Abstract |
44 |
|
10
|
Accuracy Prediction for Loan Risk Using Machine Learning Models
- Anchal Goyal, Ranpreet Kaur Abstract |
52 |
|
11
|
Securing The Cloud Resources Using Attribute Based Access Control
- Pradnya Agale Abstract |
58 |
|
12
|
Confidential Audio Transmission using Image Slicing
- Vivek Solavande Abstract |
62 |
|
13
|
Comparison of Image Search Reranking Techniques
- Ayswarya Chandramohan, Prathibha S Nair Abstract |
65 |
|
14
|
Robust Biometrics Based Authentication Scheme Using Watermarking
-Naga Sowjanya K, Kannamma R Abstract |
69 |
|
15
|
Path Planning through PSO Algorithm in Complex Environments
- Mukesh Kumar Nandanwar, Dr. Anupam Shukla, Dr. A.S. Zadagaonkar Abstract |
79 |
|
16
|
Survey on Copy Move Image Forgery Detection Techniques
- Jaseela S, Mrs. Nishadha S. G Abstract |
87 |
|
17
|
A Survey on Reversible Image Data Hiding
- Asha S Raj, Mrs.Gayathri Nair P Abstract |
92 |
|
18
|
Breaking New Grounds: Realization Of “ALL EAR” Screen Readers
- Dr. M. A. Pradhan, Shambhavi Sinha, Swarali Shirke, Vedant Deshmukh, Akhilesh Mishra Abstract |
99 |
|
19
|
Search and Safe Exchange of Real-Time Video on Mobile Cloud
- V.Pavithra, S.V.Shreekeerthana, S.Yogapriya Abstract |
103 |
|
20
|
A Design Approach for Wireless Communication Security in Bluetooth Network
- C.Suresh, V.Vidhya, E.Shamli, R.Muthulakshmi, S.Menaka Abstract |
106 |
|
21
|
Aspect-Based Opinion Mining Using Dependency Relations
- Amani K Samha Abstract |
113 |
|
22
|
Big Data: Data Driven Design philosophy for Solving Hard Optimization Problem
- Sridevi Malipatil,Vani. N Abstract |
124 |
|
23
|
A Brief Survey of Privacy Preserving Data Mining
- Shilpa M.S, Shalini.L Abstract |
131 |
|
24
|
Implementation Idea For Secure Data Deduplication Using Hybrid Cloud Approach
- Ms. Deepali C. Ghosalkar Abstract |
136 |
|
25
|
Preprocessing of Dataset for Quality Analysis of Contact Lens Material in Ophthalmology Using PCA
- Sumitra S, Dr. Ananthi Sheshasaayee Abstract |
140 |
|
26
|
Enhancing Probability of Music Selection Using Smart Shuffling Policy
- Suraj Rasal, Paras Gandhi, Shraddha Shelar Abstract |
143 |
|
27
|
Parking Availability in Sensor Enabled Car Parks
- Snehal Bankar, Mitali Dhaigude, Sonali Gajendragadakar, Supriya Gavli Abstract |
146 |
|
28
|
Watermark Extraction and Validation in Images Using Hybrid Techniques
- Chhaya Verma, Dr. Sandhya Tarar Abstract |
151 |
|
29
|
Image and Video Processing Edge Detection Technique used for Traffic Control Problem
- Himanshu Chauhan. Dr. Sandhya Tarar Abstract |
157 |
|
Under in review process... |