IJCST ONLINE
DOWNLOADS
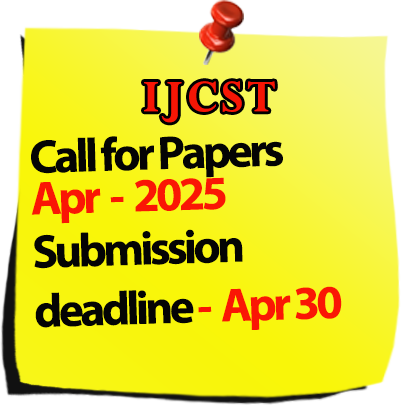
Call for Paper :

Welcomes Conference Proposals

International Journal of Computer Science Trends and Technology
IJCST-Volume 2 Issue 6 / Nov - Dec 2014
|
S.No
|
Title/Author Name
|
Page No
|
|
1
|
Reducing Web Latency through Web Caching and Web Pre-Fetching
-Rupinder Kaur, Vidhu Kiran Abstract |
1 |
|
2
|
Study Of Ethical Hacking
-Bhawana Sahare, Ankit Naik, Shashikala Khandey Abstract |
6 |
|
3
|
Study of Nature Inspired Computing
-Suraj Dewangan, Ankit Naik, Aman Agrawal Abstract |
11 |
|
4
|
A Review Of Image Fusion Using IHS With Wavelet Transform
-Neha Yadav, Shivani Shrivastri Abstract |
15 |
|
5
|
An Overview of One To One Optimization (OTOO)
-Athitha M A, Akshatha M A Abstract |
21 |
|
6
|
Paper Removed |
- |
|
7
|
Study on RFID, Architecture, Service and Privacy with Limitation
-Tanuja Dahariya, Ankit Naik, Menaka Chandra Abstract |
29 |
|
8
|
Study of Wireless Sensor Networks Security Issues and Attacks
-Menaka Chandra, Ankit Naik, Chayya Chandra Abstract |
34 |
|
9
|
Study of HADOOP
-Bhawana Sahare, Ankit Naik, Kavita Patel Abstract |
40 |
|
10
|
Image Enhancement at a Glance
-Ms. Alokita Kasu, Mr.VidyaSagar Deshmukh, Ms. Savita Agrawal Abstract |
44 |
|
11
|
Efficient Query Processing For PIM System
-U.Padma Jyothi, A.Seenu Abstract |
48 |
|
12
|
Fast and Robust Hybrid Particle Swarm Optimization TABU Search Association Rule Mining (HPSO-TS-ARM) algorithm for Web Data Association Rule Mining (WDARM)
-Sukhjit Kaur, Monica Goyal Abstract |
53 |
|
13
|
Energy Efficient Image Transmission In Wireless Multimedia Sensor Networks
-Vijay Ramaraju, P Subramanyam Raju, K Prabhakara Rao Abstract |
58 |
|
14
|
Email Clustering Using Lingo Algorithm
-Sangeeta Maharana, Minal Mohite, Pornima Wadekar Abstract |
62 |
|
15
|
Dynamic Metric For Enhancing Software Reliability And Testability Using Genetic Algorithm
-Vaid Singh, Charnpreet Kaur Abstract |
68 |
|
16
|
A Comparative Performance Analysis of High Density Impulse Noise Removal Using Different Type Median Filters
-Trapti Soni, Mrs.Vaishali Joshi Abstract |
73 |
|
17
|
A Simple Steganography Technique for Hiding Data into Image
-Satwant Singh, Proff.Lekha Bhambhu Abstract |
82 |
|
18
|
An Approach for Visual Tracking Using Background Subtraction
-Jwalita Gunda, Praveen Gugulothu Abstract |
87 |
|
19
|
Content Based Image Retrieval Using HADOOP Map Reduce
-Hinge Smita, Gaikwad Monika, Chincholkar Shraddha Abstract |
94 |
|
20
|
A Review of IRIS Recognition Method
-Neelam Singh, Mr. Lokesh Singh, Mr. Bhupesh Gaur Abstract |
97 |
|
21
|
Review of Artificial Neural Network Technique for Restoring Image
-Sumit Bhardwaj, Arun Kumar, Dr.Vinod Shokeen Abstract |
102 |
|
22
|
Image Steganography Using Optimal Random Substitution
-Satwant Singh, Proff. Lekha Bhambhu Abstract |
106 |
|
23
|
Relative Review of Automated Testing Tools: (QTP) Quick Test Professional, Selenium and Test Complete
-Tarannam Bharti, Er Vidhu Dutt Abstract |
110 |
|
24
|
Eigen Based Facial Expression Using Mouth Feature
-M Prasad, Ajit Danti Abstract |
115 |
|
25
|
GSM Mobile Authentication Based On User SIM
-Sandip Mishra, Dr. Nilesh Modi Abstract |
121 |
|
26
|
Edge Detection as an Effective Technique in Image Segmentation for Image Analysis
-Manjula KA Abstract |
126 |
|
27
|
Context-Sensitive Suggestion Inlining Designed For Java
-A. Ramalakshmi Abstract |
132 |
|
28
|
Optical and Geometrical construction of Double-Beam Spectrophotometers
-Dr. Syed Nisar Ahmed Abstract |
153 |