IJCST ONLINE
DOWNLOADS
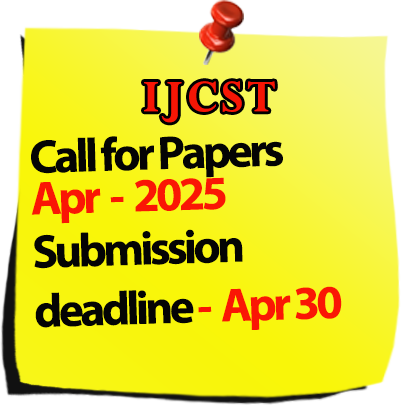
Call for Paper :

Welcomes Conference Proposals

International Journal of Computer Science Trends and Technology
IJCST-Volume 3 Issue 1 / Jan - Feb 2015
|
S.No
|
Title/Author Name
|
Page No
|
|
1
|
Various Approaches of Intrusion Detection in Heterogeneous WSN
-Ms.Smita H.Karande, Mr.S.P.Kosbatwar Abstract |
1 |
|
2
|
Technical Review of Energy Management Mechanisms in Wireless Sensor Network
-Smit D. Saraiya, Yogendra K. Patel, Urvish D. Modi, Vatsal P. Shah, Hardik A. Patel, Sandip Delwadkar Abstract |
5 |
|
3
|
Metadata Based Approach for Web Multimedia Model
-Siddu P. Algur, Basavaraj A. Goudannavar, Prashant Bhat Abstract |
11 |
|
4
|
FUZZY SQL For Linguistic Queries
-Poonam Rathee Abstract |
17 |
|
5
|
Secure Video Data Hiding Using DCT and LZW
-Kumbhar Shraddha, Rokade Varsha, Sukre Mayuri Abstract |
24 |
|
6
|
Significant Analysis of Leukemic Cells Extraction and Detection Using KNN and Hough Transform Algorithm
-Subhan, Ms. Parminder Kaur Abstract |
27 |
|
7
|
Contrasting Different Distance Functions Using K-Means Algorithm
-Kanika, Gargi Narula Abstract |
34 |
|
8
|
Data Encryption In Unreliable Clouds
-Anuradha Yenkikar, Nikhil Pandit, Shrikant Shinde, Omprakash Pawar, Sachin Rajage Abstract |
37 |
|
9
|
Efficient Performance Evaluation for Robust Eye Localization System
-Krupa Jariwala, Dr. Mrs. Upena Dalal Abstract |
40 |
|
10
|
Vehicle Parameter Monitoring Using CAN Protocol
-Pratiksha Nawale, Anjali Vekhande, Priyanka Waje Abstract |
46 |
|
11
|
Interconnection between Peripherals in SoC'S Using CDMA Technique
-K. Shankar, T. Dineshkumar Abstract |
50 |
|
12
|
Security Applications for Malicious Code Detection Using Data Mining
-Suvendu Jena, Eshwari Kulkarni, Namrata Annaldas, Pravin Yalameli, Karishma Shingade Abstract |
56 |
|
13
|
OQM Model: A Case Study of Software Quality
-Mrs. Neha Agrawal Abstract |
62 |
|
14
|
A Highest Response Ratio Next(HRRN) Algorithm based Load Balancing Policy for Cloud Computing
-Rakesh Kumar Sanodiya, Dr. Sanjeev Sharma, Dr. Varsha Sharma Abstract |
72 |
|
15
|
Network Load Balancing and Its Performance Measures
-Ms. Arti Mishra Abstract |
77 |
|
16
|
An Overview of Data Mining and Warehousing – Architecture, Techniques and Applications
-P.Nithya, G.Lakshmipriya Abstract |
82 |
|
17
|
Agile Software Development Technological Implementation: Apache Struts Suitability
-Nitin Goel, Sudheer Kr Singh, Shashank Singh, Sameer Dixit Abstract |
87 |
|
18
|
Web Based Custom Validation Using Framework in Java
-Dr Ankur Saxena Abstract |
90 |
|
19
|
An Overview of CDMA Correlation Techniques in 3G Systems
-Ms. S. Chitra Abstract |
97 |
|
20
|
Campus Guidance and Security Application
-Prof.Santosh Pawar,Rahul Doke,Abhimanyu Jadhav,Mahaveer Khaire,Tejas Jawalkar Abstract |
101 |
|
21
|
A Study on Algorithmic Approaches and Mining Methodologies In Data Mining
-S. Padmapriya Abstract |
105 |
|
22
|
Concentration on the Area of Significance in Medical Images
-Jinesh K. Kamdar, Pritam A. Amre, Chintan B. Khatri, Prof. Mahendra S. Patil Abstract |
110 |
|
23
|
An Implementation of Improving the Service Accessibility for Cloud Users by Using Traffic Redundancy Elimination (TRE) Mechanism with PACK Technique
-Ms. R.Poorvadevi. A.Lakshmidurga, Ms.D.SaiVijitha, Ms. J.Praseeda Abstract |
115 |
|
24
|
A Survey on Cloud Computing Security and Solutions
-N. Sugavaneswaran, D.Saravanan Abstract |
124 |
|
25
|
Functionality Appraisal of Automated Testing Tools
-Tarannam Bharti, Er Vidhu dutt Abstract |
129 |
|
26
|
Data Generation for Analytics in HADOOP
-Anjali Devi, Aarif Birajdar, Madhuri Pol, Shobha Halle, Safiya Shaikh, Savita Halle Abstract |
135 |
|
27
|
Data Sharing in Cloud Storage by RSA based Encryption
-S. Monika, M. Jawahar, S.K. Murugaraja Abstract |
140 |
|
28
|
A Survey on Multi-Stage Interconnection Networks
-Dr. Harsh Sadawarti, Sony Bansal, Nirlaip Kaur Abstract |
143 |
|
29
|
Discovery and Visualization of Patterns in Data Mining Through Python Language
-Shipra Bansal, Nitin Bansal Abstract |
152 |
|
30
|
Designing of an Application on Health Development based on Android Platform
-Pallavi Gaur, Gopal Krishan Prajapat Abstract |
161 |
|
31
|
Reviewing execution performance of Association Rule Algorithm towards Data Mining
-Dr. Sanjay Kumar, Abhishek Shrivastava Abstract |
165 |
|
32
|
Performance Enhances Test Case Prioritization for Regression Testing
-Al Mehedi Hasan, Sheena Singh Abstract |
172 |
|
33
|
Comparison between Square Pixel Structure and Hexagonal Pixel Structure in Digital Image Processing
-Illa Singh, Ashish Oberoi Abstract |
176 |
|
34
|
A Review of Hybrid Intrusion Detection System
-Pushpak Singha, Anup Sheth, Rahul Lakkadwala, Akshay D. Gaikwad, Megha V. Kadam Abstract |
182 |
|
35
|
Handwritten Signature Verification based on SURF Features using HMM
-Ms Rajpal Kaur, Ms. Pooja Choudhary Abstract |
187 |
|
36
|
Joint Relay and Jammer Selection for Secure Two-Way Relay Networks
-Prof. Ms. Gulnaz Thakur, Prof. Trupti Dhumal, Prof. Ms. Ifra Kaladgi, Prof. Ms. Asiya Khan Abstract |
196 |
|
37
|
Routing Issues in Mobile Ad Hoc Networks: A Survey
-Meena Rao, Neeta Singh Abstract |
200 |
|
38
|
Sentiment Classification by Semantic Orientation Using SentiWordNet Lexicon from Online Customer Reviews
-Monalisa Ghosh, Prof (Dr) Gautam Sanyal Abstract |
206 |