IJCST ONLINE
DOWNLOADS
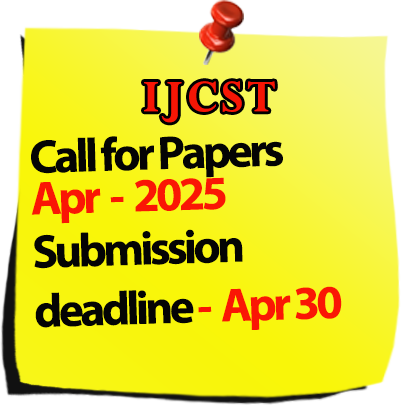
Call for Paper :

Welcomes Conference Proposals
International Journal of Computer Science Trends and Technology
IJCST-volume-13 Issue 3 / May-Jun 2025
|
S.No
|
Title/Author Name
|
Page No
|
|
1
|
Research on E-commerce Platform of Online Shopping Consumers
- Aastha Tyagi, Khushee Tyagi, Sushant Pal, Parteek Sharma  10.33144/23478578/IJCST-V13I3P1
10.33144/23478578/IJCST-V13I3P1
[Abstract] [ 
|
1 |
|
2
|
Online book store
- Apurva Mahato,Vikas,Shivam  10.33144/23478578/IJCST-V13I3P2
10.33144/23478578/IJCST-V13I3P2
[Abstract] [ 
|
7 |
|
3
|
E-Donation in India: Trends, Challenges, and Opportunities
- Sumit Dutt, Aanchal Rao, Sadhana Kumari, Sonali  10.33144/23478578/IJCST-V13I3P3
10.33144/23478578/IJCST-V13I3P3
[Abstract] [ 
|
14 |
|
4
|
Enhancing Cloud Security: A Review of Hybrid Intrusion Detection Approaches
- Himanshu Jaiswal, Sreeja Nair, Ritu Ranjani Singh  10.33144/23478578/IJCST-V13I3P4
10.33144/23478578/IJCST-V13I3P4
[Abstract] [ 
|
21 |
|
5
|
ML DJango Framework Integration for IOT Attacks
- Mr.Gokulnath D, Ms.Fathima G  10.33144/23478578/IJCST-V13I3P5
10.33144/23478578/IJCST-V13I3P5
[Abstract] [ 
|
29 |
|
6
|
Entity Recognition by Natural Language Processing and Machine Learning
- Sharmila Dalave, Prof. S. A. Gaikwad  10.33144/23478578/IJCST-V13I3P6
10.33144/23478578/IJCST-V13I3P6
[Abstract] [ 
|
34 |
|
7
|
A Brief Study on Formulation of Some Transportation Problem in Linear Programming
- Anil Raj, Dr. Krishnandan Prasad  10.33144/23478578/IJCST-V13I3P7
10.33144/23478578/IJCST-V13I3P7
[Abstract] [ 
|
38 |
|
8
|
Object Detection Techniques: A Review
- Tanuj Kumar Bharadwaj, Shubham Sharma  10.33144/23478578/IJCST-V13I3P8
10.33144/23478578/IJCST-V13I3P8
[Abstract] [ 
|
45 |
|
9
|
Power Business Intelligence Developed by Microsoft: A Case Study
- Amit Kumar Singh, Ankita Kumari, Anit Tyagi, Tanisk Tyagi, Ashutosh Pradhan  10.33144/23478578/IJCST-V13I3P9
10.33144/23478578/IJCST-V13I3P9
[Abstract] [ 
|
54 |
|
10
|
Facial Expression Based Stress Detection Using Machine Learning
- Rishabh Biltoriya, Sagar, Sachin Singh, Mohit updhyay  10.33144/23478578/IJCST-V13I3P10
10.33144/23478578/IJCST-V13I3P10
[Abstract] [ 
|
66 |
|
11
|
Deep Fake Image Detection Using Supervised Machine Learning Technique: A Study
- Sharad Shrivastava, Prof. Sandeep Piplotia  10.33144/23478578/IJCST-V13I3P11
10.33144/23478578/IJCST-V13I3P11
[Abstract] [ 
|
72 |
|
12
|
DEA-RNN: A Hybrid Deep Learning Approach For Cyberbullying Detection in Twitter Social Media Platform
- Bujunuru Sudheer Kumar, Dr.s. Latha  10.33144/23478578/IJCST-V13I3P12
10.33144/23478578/IJCST-V13I3P12
[Abstract] [ 
|
78 |
|
13
|
Incremental Core Transformation: A Modular First Approach to Legacy Modernization in Banking
- Ashish G. Vishwakarma  10.33144/23478578/IJCST-V13I3P13
10.33144/23478578/IJCST-V13I3P13
[Abstract] [ 
|
83 |
|
14
|
Botnet Attack Prevention in Internet of Things (IOT) Devices Using AI
- Sanjeev Kumar, Prof. Shivank Soni  10.33144/23478578/IJCST-V13I3P14
10.33144/23478578/IJCST-V13I3P14
[Abstract] [ 
|
91 |
|
16
|
Python-Based Detection of Paddy Leaf Diseases: A Computational Approach
- Srikant Singh, Ekta Jayantibhai Patel, Rohit Kumar Awasthi  10.33144/23478578/IJCST-V13I3P16
10.33144/23478578/IJCST-V13I3P16
[Abstract] [ 
|
104 |
|
17
|
Self-Attention Mechanisms for Detecting Anomalies in Encrypted Network Traffic: A Systematic Review
- Sabuhee, Pratik Buchke  10.33144/23478578/IJCST-V13I3P17
10.33144/23478578/IJCST-V13I3P17
[Abstract] [ 
|
114 |
|
18
|
Experimental Analysis of Classical Segmentation Technique for Bacterial Colony Counting
- M. Sivapriya, N. Senthilkumaran  10.33144/23478578/IJCST-V13I3P18
10.33144/23478578/IJCST-V13I3P18
[Abstract] [ 
|
126 |
|
19
|
Advancing Software Quality through Hybrid CNN-LSTM Bug Prediction: Beyond Traditional Models
- Rinku Taide, Imran Ali Khan  10.33144/23478578/IJCST-V13I3P19
10.33144/23478578/IJCST-V13I3P19
[Abstract] [ 
|
135 |
|
20
|
IPv4 vs. IPv6: Migration Challenges and Solutions
- Dr.Mohammed Iliyas  10.33144/23478578/IJCST-V13I3P20
10.33144/23478578/IJCST-V13I3P20
[Abstract] [ 
|
149 |
|
21
|
Real-Time Operating Systems for Safety-Critical Applications (e.g., Drones, Medical Devices)
- Dr.Mohammed Iliyas  10.33144/23478578/IJCST-V13I3P21
10.33144/23478578/IJCST-V13I3P21
[Abstract] [ 
|
154 |
|
Under in review process... |